How to get more out of your free Burp Suite Community Edition?
Alright, let’s start with something important. Do not use any sort of cracked version of Burp Suite Professional. Using illegally acquired software is not cool. Also, Portswigger (the company behind Burp Suite) is just super awesome to the community. This most of all starts with the community edition offering that comes entirely for free! Apart from that, they have the absolute best free web app sec training existing on the market.
However, the community edition does indeed have quite heavy limitations. In this blog post, we are going to look into a couple of examples. I am going to show you how you can overcome those restrictions to some extent!
Search
Yes, something as simple as searching for a specific string or using a regex to find the needle in your big stack of recorded requests goes a long way towards successful exploitation.
Portswigger thinks so too and does not allow you to do that.
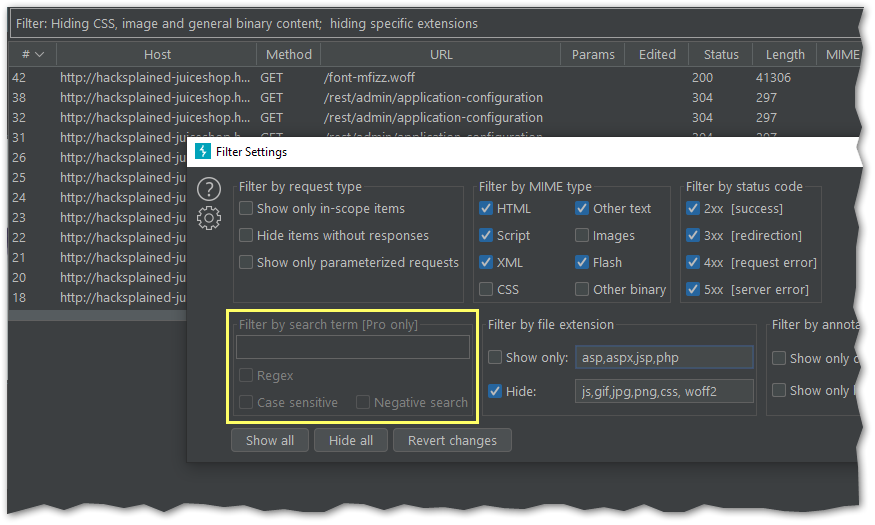
Fortunately, there are absolutely superb extensions that not just add the search functionality, but also provide more features that the current Burp filter does not have.
Flow
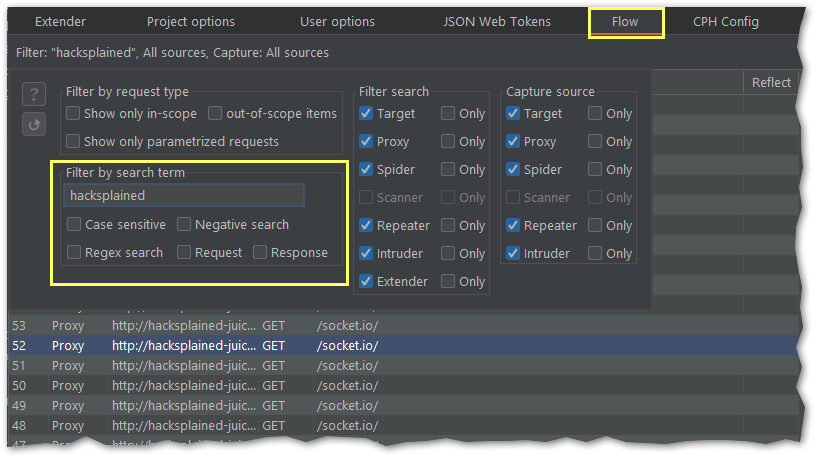
Find out more about Flow and its feature set here.
Logger++
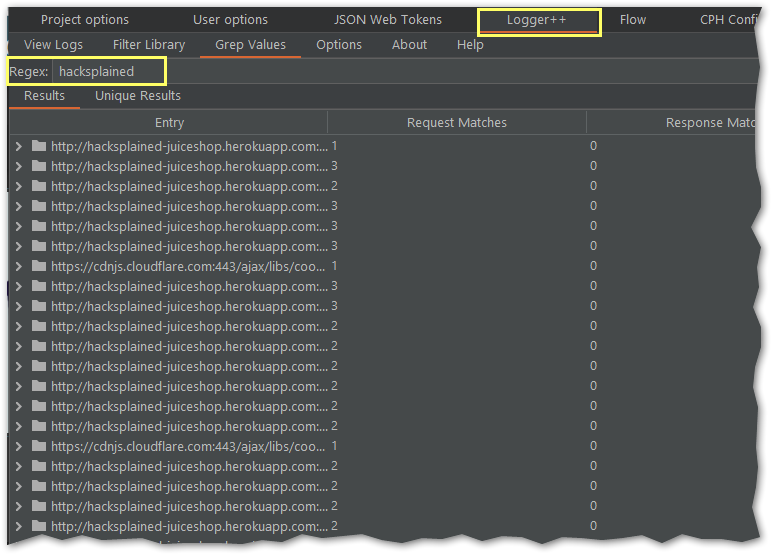
Find out more about Logger++ and its feature set here.
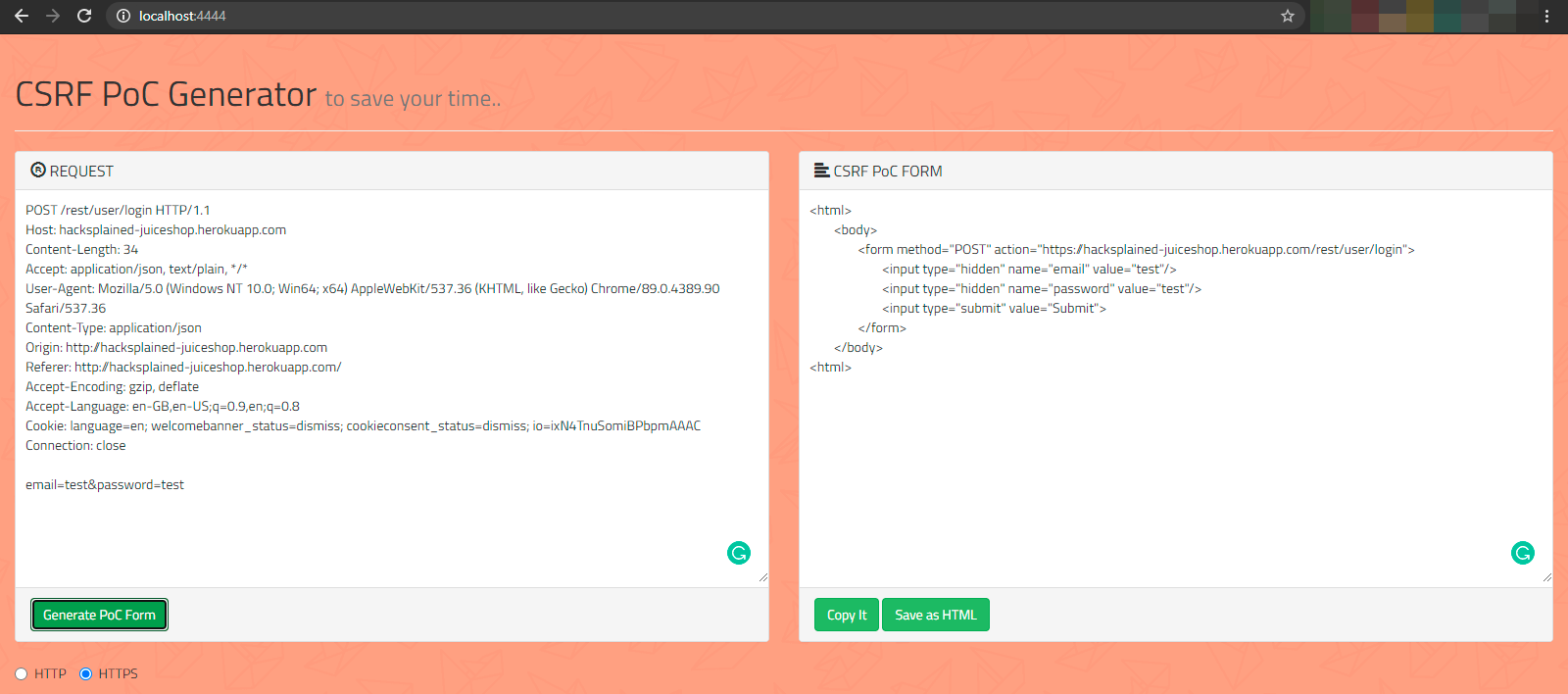
Generate CSRF POC
Burp Suite Professional has this amazing feature where you can right-click on any request and create a CSRF POC (proof-of-concept). This is super handy during testing as it saves you time to write the .html file by yourself. Read more about the feature here.
However, CSRF POCs can fortunately be crafted quite easily. Make sure to have a pre-built CSRF POC template ready to use or check out this Github project by Mert Tasci. You can just git clone the repository and run it with python3 -m http.server. After that, copy the request in question and insert it into the CSRF generator.
Burp Collaborator
I gotta say, the integrated Burp Collaborator definitely is the coolest feature in my opinion. This tool basically allows you to quickly check for e.g. SSRF (server-side request forgery) vulnerabilities by showing you all incoming DNS/HTTP/SMTP traffic.
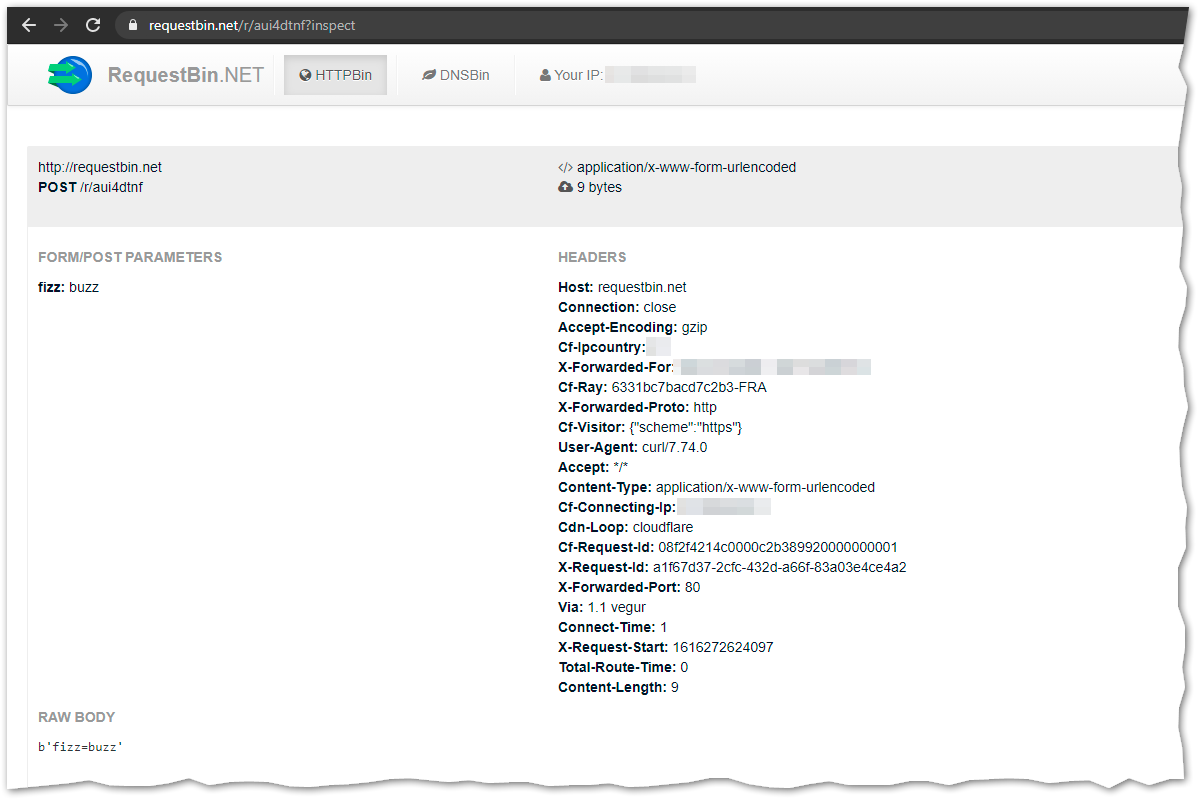
It would not be part of this blog post though, if there would not be an excellent alternative. If you are all about monitoring HTTP or DNS queries, requestbin.net is a pretty good substitute that comes entirely for free.
Burp Intruder
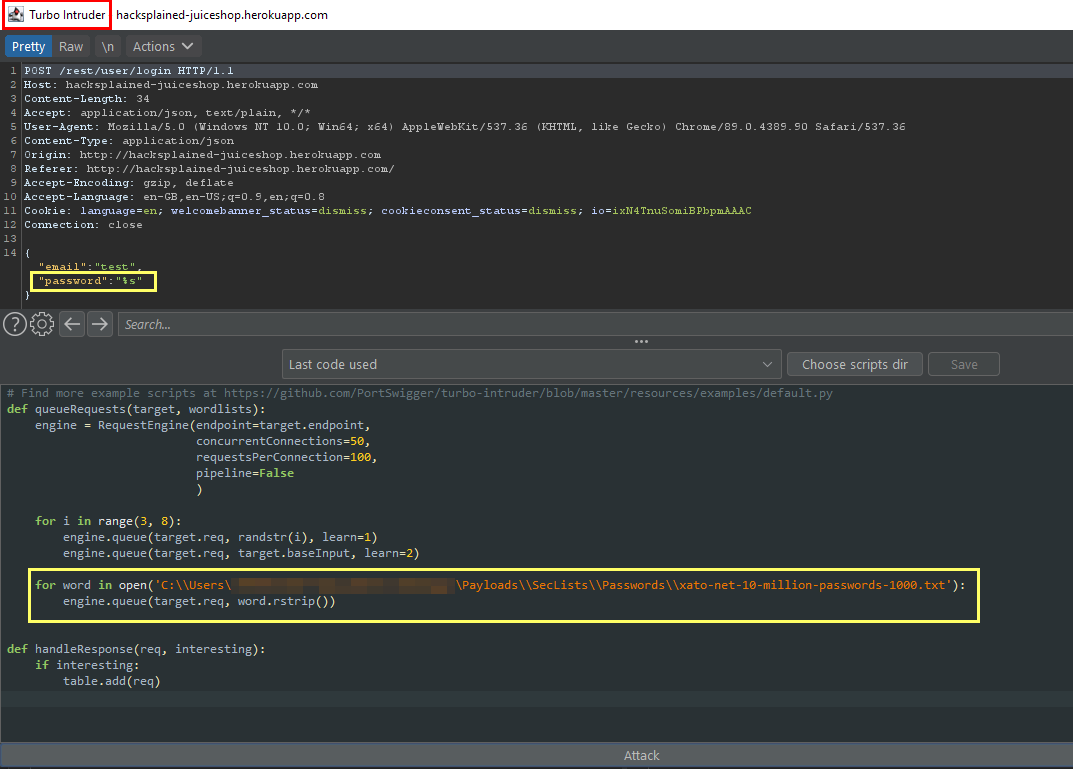
Burp Suite’s Intruder generally speaking is part of the community edition. However, the big drawback is the request throttling in place. The community edition allows you to send approximately 1 request per second. If you think of e.g. a password enumeration attack, you would probably sit in front of your computer for longer than planet Earth’s current existence.
Luckily, there is a Burp extension called Turbo Intruder that directly comes from the man himself, James Kettle (who btw works for Portswigger).
Burp Scanner
Some people say that Burp Scanner is the heart of the entire product. I do agree to some extent but at the same time heavily disagree. One the one hand, the scanner is a compound of excellent web application crawling technology (Burp just recently outlined the inner workings of their crawler here) and an automated vulnerability scanning capability. On the other hand, it is not the feature I use most often. I actually barely use it at all.
The crawling and scanning engine are both nicely integrated in Burp’s UI but can once again be substituted with different tools. In regards to crawling, I am personally a fan of clicking through the entire web app by myself anyway. Whenever you start a penetration test or when you are going for bug bounties, make sure to fire up Burp and start browsing. This is not just feeding Burp’s proxy tab, but also immediately gives you a great first glimpse of the application’s behavior and purpose.
Some of you might say now “… but not all pages are directly linked”. That’s absolutely correct. For discovering unlinked directories and paths, I recommend to use a tool called FFUF. You can check out e.g. InsiderPhD’s video on how to use that tool.
In regards to scanning, the best and most critical vulnerabilities still have to be found manually. While we currently see a lot of active development around pentest automation, vuln categories like business logic errors will most likely always need an actual brain figuring out the issue.
The entire security community however has built hundreds of open-source tools that automate pentesting to some extent. All those tools (which cannot be mentioned in this single blog post, check out this Github repository for a start) can cover parts of Burp’s automated scanner. If you are all about payloads, then PayloadAllTheThings is the place to start looking.
In the end, Burp’s scanner is still really nice though, especially as it is displaying all the findings in an easy-to-understand way in the Dashboard tab. Check out this page to get a rough idea what the scanner is covering.
Conclusion
Portswigger’s Burp Suite is arguably one of the TOP-5 pentest tools used by the entire IT-Security community. Next to its comprehensive feature set, it also comes with a very low price tag. An annual subscription is only setting you back USD 399,–.
If you happen to be able to afford a Professional license, I can only recommend you to get it. If you are just starting out, or you are only hacking occasionally, then there is no need to go pro. Make use of the additional tools mentioned in this article to work around the limitations of Burp Suite Community.



